Lacework Infra
Lacework provides cloud security and infrastructure vulnerability detection through its cloud-native platform. In Invicti ASPM, the Lacework Infra integration connects to your Lacework environment to import infrastructure vulnerability findings by account.
Prerequisites
| Field | Description |
|---|---|
| Key ID | Lacework API key ID generated in the Lacework console |
| Secret | Lacework API secret paired with the Key ID |
| URL | The base URL of your Lacework instance (e.g., https://<account>.lacework.net) |
How to Get a Key ID and Secret (on Lacework Side)
- Log in to the Lacework console.
- Navigate to Settings > API Keys.
- Click + Create New.
- Enter a name and description for the key.
- Click Save. Download or copy the Key ID and Secret immediately — the secret is shown only once.
Note: Refer to the Token Instructions link displayed in the Invicti ASPM settings panel for additional guidance on generating Lacework API credentials.
Step 1: Navigate to Integrations
From the left sidebar menu, click on Integrations.
Step 2: Select the Infra Tab
On the Integrations > Scanners page, click on the Infra tab.
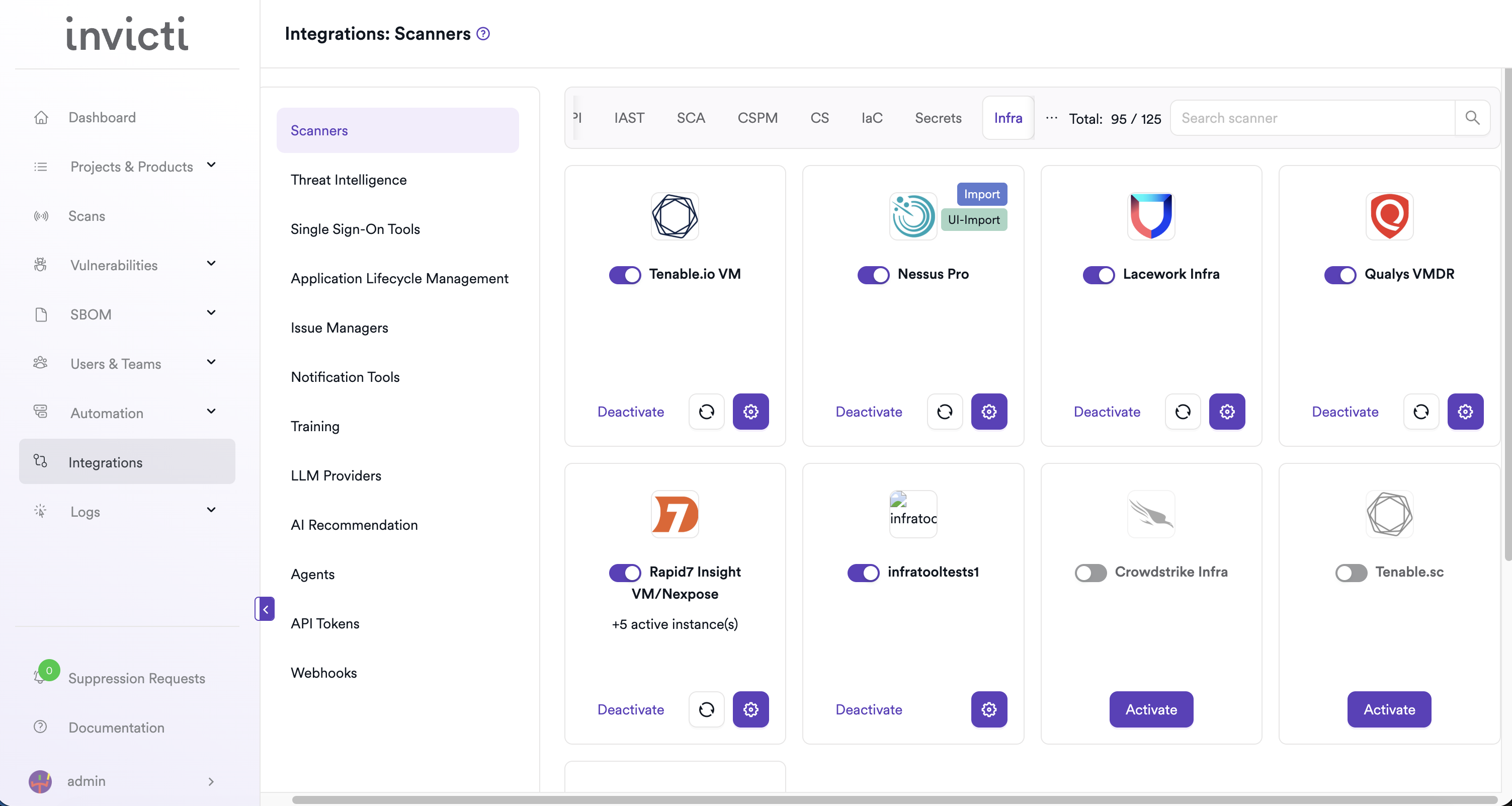
Step 3: Find and Activate Lacework Infra
Scroll through the list of Infra scanners to find Lacework Infra.
- If Lacework Infra is not activated, click the Activate button to enable the integration.
Step 4: Configure Connection Settings
Click the gear icon on the Lacework Infra card to open the settings panel. Fill in the required fields:
| Field | Description | Required |
|---|---|---|
| Key ID | Lacework API Key ID | Yes |
| Secret | Lacework API Secret paired with the Key ID | Yes |
| URL | Base URL of your Lacework instance | Yes |
| Insecure | Skip TLS certificate verification (use only for self-signed certificates) | No |
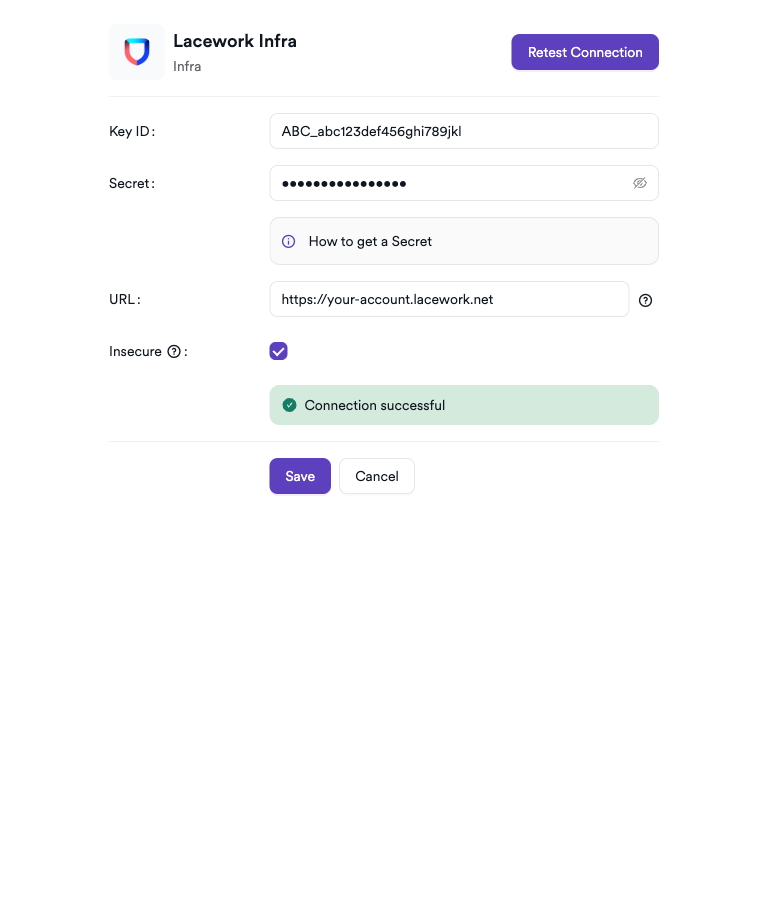
Step 5: Test the Connection
Click Test Connection. A green Connection successful message confirms that Invicti ASPM can authenticate with the Lacework API.
Summary
| Step | Action |
|---|---|
| 1 | Navigate to Integrations from the sidebar |
| 2 | Select the Infra tab |
| 3 | Activate Lacework Infra |
| 4 | Enter Key ID, Secret, and URL |
| 5 | Test the connection |
How to Create a Scan
Navigate to Project Scanners
- Open a project in Invicti ASPM.
- Go to Settings > Scanners.
- Click Add Scanner.
Add Lacework Infra Scanner
- Select Infra as the scanner type.
- Choose Lacework Infra from the scanner list.
- Click Add to open the scan configuration drawer.
Scan Configuration Fields
| Field | Description | Required |
|---|---|---|
| Profile Name | A name to identify this scan configuration | Yes |
| Account ID | Select the Lacework account to associate with this scan | Yes |
| Meta Data | Additional metadata to tag the scan | Yes |
| Scan Tag | Free-text tag to identify or group scans | No |
| Severity+ | Increase severity of imported findings by one level | No |
| Severity- | Decrease severity of imported findings by one level | No |
Account ID links the Invicti ASPM project to a specific Lacework account. Infrastructure vulnerability findings tracked under that account will be imported into the project.
Severity+ and Severity- are mutually exclusive — only one can be enabled at a time.
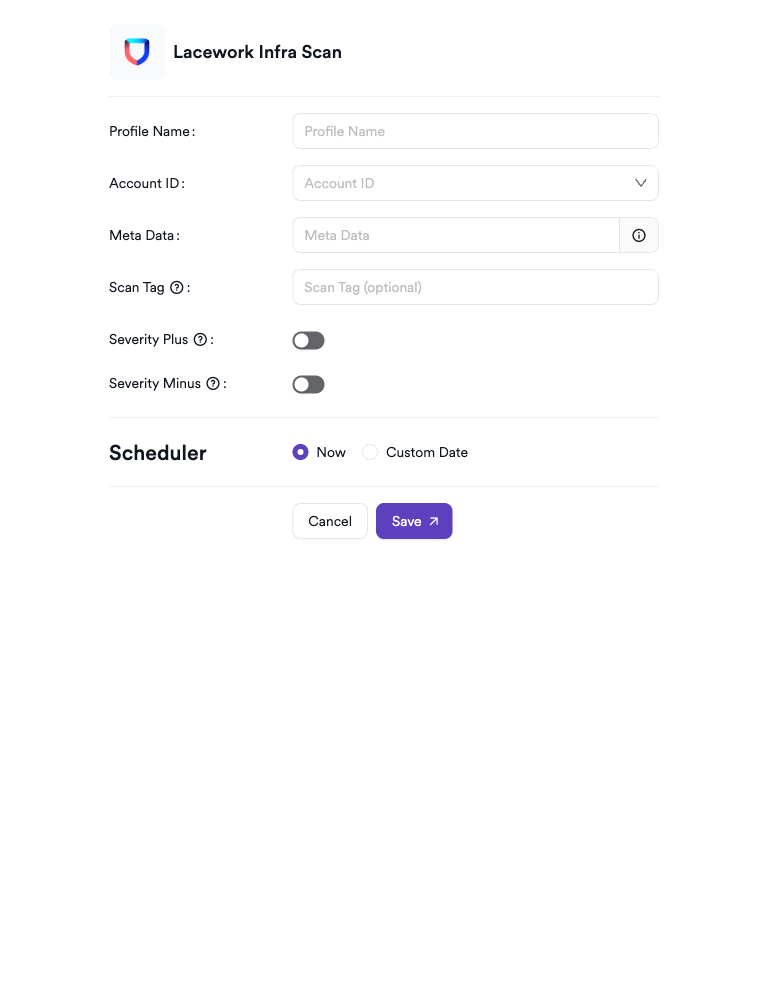
Scheduler
Enable the Scheduler toggle to automatically run Lacework Infra scans on a recurring schedule.
Webhook (Optional)
Add a webhook URL to receive scan completion notifications.
KDT Command
kdt scan -p <project_name> -t laceworkinfra -b -Troubleshooting
Connection Fails
| Issue | Resolution |
|---|---|
| Invalid Key ID or Secret | Verify the credentials in the Lacework console under Settings > API Keys. Regenerate if needed. |
| URL unreachable | Confirm the Lacework instance URL (https://<account>.lacework.net) is reachable from the Invicti ASPM server. |
| TLS certificate error | If using a self-signed certificate, enable the Insecure option in the connection settings. |
| Secret not available | The secret is shown only at creation — create a new API key if the original was not saved. |
Scan Issues
| Issue | Resolution |
|---|---|
| No accounts available in Account ID dropdown | Ensure the API key has access to at least one Lacework account and that infrastructure vulnerability data is available. |
| Scan shows no findings | The account may have no known vulnerabilities, or Lacework assessments may not have completed yet. Check the Lacework console. |
| Scan not starting | Verify the scanner is activated and the connection test passes in the integration settings. |
Best Practices
- Use a dedicated API key for Invicti ASPM with the minimum required permissions rather than reusing credentials shared with other tools.
- Rotate the Secret periodically and update the integration settings in Invicti ASPM accordingly.
- Associate each Invicti ASPM project with the Lacework account that tracks its production infrastructure for accurate vulnerability data.
- Use the Scheduler to align scans with your Lacework assessment cadence so findings always reflect the latest state.
Limitations
- Lacework Infra in Invicti ASPM imports vulnerability data from existing Lacework infrastructure assessments — it does not trigger new Lacework scans.
- Only accounts accessible via the provided API key are available for selection.
- Runtime behavioral signals and cloud activity findings from Lacework are not surfaced in Invicti ASPM; only infrastructure vulnerability data is imported.
Updated about 2 months ago
